| Version 1 (modified by , 4 years ago) ( diff ) |
|---|
Ideas sobre la Seguridad en las Comunicaciones Digitales que las personas activistas deberían tener presente
¡La situación de cada persona es diferente! Pero hay temas comúnes y podemos aprender de cada una.
Temas Básicos
La Seguridad no es sólo una cosa. Puedes pensar acerca de los riesgos que enfrentas de manera más clara si entiendes las preocupaciones que tienes. Cuatro temas relevantes sobre seguridad en los que vale la pena pensar son:
- Privacidad
- ¿Quién puede ver mis comunicaciones?, ¿son sólo las personas que deberían?, ¿qué significa la privacidad cuando el mismo mensaje es enviado a varias personas?, ¿quién puede violar la privacidad?, ¿estoy protegiendo la privacidad de mis miembros o de las personas con las que estoy trabajando?
- Autenticidad
- Cuando recibo mensajes, ¿cómo se quién son?, ¿son realmente de esa persona?; cuando comunico mensajes en los que mi identidad es importante y relevante, ¿cómo pueden las personas con las que me estoy comunicando saber que los mensajes efectivamente son míos?
- Anonimato
- Cuando quiero comunicarme sin divulgar mi identidad (con puede ser el caso de las denuncias anónimas), ¿cómo puedo asegurarme de que mi identidad está protegida?
- Confiabilidad y acceso
- ¿El medio de comunicación que estoy usando es confiable?, ¿quién controla el medio?, ¿puede ser apagado o interrumpido su funcionamiento?, ¿estará disponible cuando lo necesite urgentemente?
Discutir estos temas con tus compañeros y compañeras organizadores y activistas es un excelente primer paso para la construcción de seguridad. Ten en mente que las mejoras en un área (como la privacidad) pueden conducir a una disminución de la seguridad en otra área (como la confiabilidad y el acceso).
Un recurso que podrías encontrar útil es una hoja de trabajo desarrollada por Progressive Technology Project. Intenta completar ambas páginas.
También podrías estar interesado o interesada en el Tutorial de Seguridad de Riseup y en la visión general de algunas herramientas propuestas.
Traducción pendiente
Live Meetings
Our movement is increasingly reliant on live, online meetings. Corporations are spending hundreds of millions of dollars perfecting Internet video calls, however, the dangers of surveillance and corporate control makes these options poor choices for movement organizers and activists.
We recommend:
- mumble for audio-only conferences for up to hundreds of people at the same time, with the ability to intergrate a live Interpreter.
- jitsi meet for video conferences of up to 20 people.
For more information about live meetings, please see our Spring 2020 statement.
Sending messages
One activity we engage in every single day is sending each other messages. Sending messages crosses all four themes, so picking the right method will depend on, for example, how you compare your need for privacy with your need for reliability.
Email is the oldest and most universal form of exchanging messages.
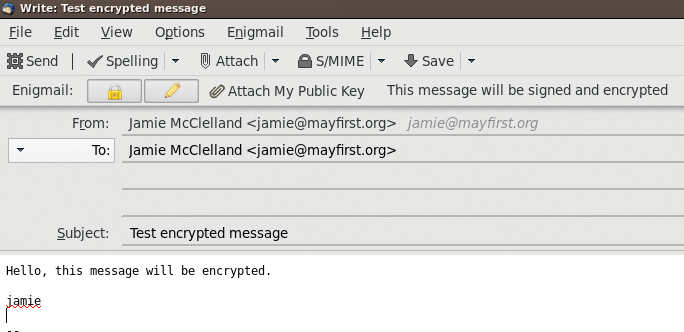
- OpenPGP is a method that allows you to encrypt your messages in a way that not even your Internet provider can decipher them. You can encrypt messages via your desktop email program or one used on your phone. However, it is hard to setup and requires both you and the recipient are using it
Example of writing an encrypted email in the Thunderbird email program using engimal.
- How do you get your email? Webmail means going to a web site and entering your username and password to access your email. It is very convenient, you can access your email anywhere even if you don't have your phone or computer. However, it also means that all of your email is saved on the server, which could be subpoenaed. Alternatively, you can use a desktop or mobile client that downloads your email, removing it from the server. However, your phone or computer can be lost or subpoenaed. There is no right answer! But at MF/PL you can choose between webmail or a client based on your needs.
Other forms of instant messaging
- All May First/People Link members can use jabber - which works on your computer and on your phone and supports end-to-end encryption.
Example of writing an end-to-end encrypted message using the gajim program vi the Jabber network
- Another popular, free and secure messaging applications is called Signal by Whisper Systems.
Web sites
Web sites also cross many different security themes. Your web site may contain sensitive data that should only be scene by people with the right access. Also, your web site may track visitors, which could be used in a lawsuit to against your allies. And lastly, web sites are the most popular target of denial of service campaigns - when your political opponents try to shutdown your web site using legal or technical measures.
- If your web site address does not have a padlock next to it (and is not accessible via https) - then all traffic to and from your site is in plain text and can be watched by anyone with the legal or technical means to intercept it. If you use a username and password to login to your site - that information is also sent without encryption. At May First/People Link, you can enable encryption with a few clicks thanks to Lets Encrypt.
- If you are using your site to organize people, and your campaign is successful, you could find yourself under criminal investigation in which logs of every visitor to your site are subpoenaed. Find out how to turn off logging on your site to avoid being placed in this position.
- May First/People link has an extensive backup system in place. However, if downtime is critical, we encourage you to mainain your own backup as well. Deciding your backup strategy will require a trade-off between privacy (you don't want backup copies lying around) and reliability (you want to have the data to get your site back online at a moment's notice)
- Many campaigns are shutdown right when they are gaining momentum due to legal take down notices. If you are running a campaign that involves a spoof or any content that could even just barely be considered illegal, please check in with us first so we can involve our generous pro-bono lawyers at the Electronic Freedom Foundation. We have a web page documenting our history fighting legal threats - something you should expect from any organization providing digital services.
- Other campaigns are shutdown due to a technical denial of service attack - when anonymous attackers flood your web site with so much data that it stops working properly. We work closely with Deflect - a DDOS protection service and have extensive experience fending off these attacks.
Databases
The movement is increasingly depending on databases specicially designed to help us organize. A database can help us track donors, send email communications, register people for events, generate phone lists and walk lists and more.
One database used throughout the movement is CiviCRM - a free and open software project that you can host within your May First/People Link account.
Due to it's complexity, many organization choose to work with a partner to set it up. For example, the Progressive Technology Project launched the PowerBase project to facilitate setting this up.
Example of search results from PowerBase
When hosting your database with a corporate provider, like Nation Builder or Saleforce, you run the risk of having your data subpoenaed without your knowledge.
Sharing Files
Sharing files is critical to movement building - whether it is allowing others to download statements or images, to providing a space for collaborative editing.
- Real-time editing or notetaking. Riseup's Etherpad instance is an excellent place for join note taking or collaborative editing. Several peole can edit the same document and see each other's edits as you type. Riseup deletes all pads that have not been edited in over a month - so be sure to copy down any completed documents.
- Similarly - May First/People Link provides a similar site for spread sheets called Ethercalc.
- For more long term document sharing, May First/People Link offers Nextcloud - a full featured site that allows you to:
- Synchronizes and share documents via the web, on your computer and on your phone
- Synchronize and share calendars between team members and your phones and computer calendars
Sharing a file via nextcloud
Attachments (5)
- gajim.png (37.6 KB ) - added by 4 years ago.
- nextcloud.png (39.3 KB ) - added by 4 years ago.
- encrypted-email.png (57.7 KB ) - added by 4 years ago.
- powerbase.png (49.4 KB ) - added by 4 years ago.
- lock.png (13.0 KB ) - added by 4 years ago.
Download all attachments as: .zip